
Cyber Security - MSc
Currently viewing course to start in 2024/25 Entry.
The MSc Cyber Security course provides a broad foundation for Cyber Security concepts while delivering advanced knowledge and skills in key technical areas....
- Level Postgraduate Taught
- Study mode Full Time/Part Time
- Location City Centre
- Award MSc
- Start date September 2024, January 2025
- Fees View course fees
- School School of Computing and Digital Technology
- Faculty Faculty of Computing, Engineering and The Built Environment
This course is:
Open to International Students
Overview
The MSc Cyber Security course provides a broad foundation for Cyber Security concepts while delivering advanced knowledge and skills in key technical areas. Designed to meet the growing demand from global business and industry for robust cyber security systems, this course underpins the principles and practical professional skills you’ll need to meet the future challenges faced by organisations, particularly when it comes to strategic security planning.

Introducing STEAMhouse
STEAMhouse is a centre for technology, innovation, creative thinking, prototyping and business development. Our brand new £70 million pound building is the new home for the School of Computing and Digital Technology.
What's covered in this course?
This course provides future Cyber Security professionals with the knowledge and skills needed by the employers. Our strong links with industry enable us to teach the most demanding topics. You will develop state of the art technical knowledge, intellectual know-how, management capabilities and hands-on practical skills to succeed in meeting the Cyber Security challenges faced by modern organisations.
Our academic staff members are actively engaged with government and industry to help solve their complex problems. These strong links provide you with plenty of professional opportunities that will help you to acquire valuable exposure to the real life challenges of Cyber Security.
Accredited By
This course is accredited by:
Why Choose Us?
-
At the forefront of advancing information security - Our Centre for Cyber Security is at the forefront of advancing information security.
-
Research-led, practice-driven teaching - Our teaching is underpinned by our versatile research projects and strong industry links.
-
Experienced academic staff - Our teaching staff have rich professional experience and are engaged with government and industry, helping to solve complex problems.
-
State-of-the-art equipment and laboratories - Our industry-standard facilities enable access to forensic software, network security software for penetration testing, and Cloud software.
-
Home to Cisco, Oracle and Microsoft Academies - We are one of Microsoft’s top UK university-based academies and we are a member of the Microsoft Developer Network Academic Alliance. We are also a Cisco ASC (Academy Support Centre) and one of only 10 Cisco Instructor Training Centres (ITC) in the UK.
- Accredited by BCS, The Chartered Institute for IT - The course meets standards set by the profession.
Similar Courses
OPEN DAY
Join us on campus where you'll be able to find out more about your course, learn about postgraduate finance and get an insight into studying at BCU. Booking for the next event isn’t open yet. Register your interest below and we’ll email you as soon as booking goes live.
Next Event: 29 June 2024
Entry Requirements
Essential requirements
Essential Requirements
|
We would normally expect you to hold at least a Second Class Honours degree or equivalent in Computing, Engineering or Information Management. |
|
Applicants without standard entry qualifications but with extensive industrial experience could be considered if they provide evidence of the necessary knowledge and skills to successfully complete the course. |
Additional information for EU/International students
| Essential |
|---|
|
International applicants are required to have IELTS overall band of 6.0 or equivalent. |
If you have a qualification that is not listed, please contact us.
Fees & How to Apply
UK students
Annual and modular tuition fees shown are applicable to the first year of study. The University reserves the right to increase fees for subsequent years of study in line with increases in inflation (capped at 5%) or to reflect changes in Government funding policies or changes agreed by Parliament. View fees for continuing students.
Award: MSc
Starting: Sep 2024
- Mode
- Duration
- Fees
- Full Time
- 12 months
- £9,710 in 2024/25
- Full Time
- 18 months with Professional Placement*
- £10,685 in 2024/25
- Part Time
- 20 months
- Show fees
- £1079 per 20 credits
- Year 1 - 80 credits
- Year 2 - 100 credits
Fees for Part-time students
This course can be studied on a Part-time study basis. The cost per year of study is based on credit requirements for that year.
Award: MSc
Starting: Jan 2025
- Mode
- Duration
- Fees
- Full Time
- 12 months
- £9,710 in 2024/25
- Full Time
- 18 months with Professional Placement*
- £10,685 in 2024/25
International students
Annual and modular tuition fees shown are applicable to the first year of study. The University reserves the right to increase fees for subsequent years of study in line with increases in inflation (capped at 5%) or to reflect changes in Government funding policies or changes agreed by Parliament. View fees for continuing students.
Award: MSc
Starting: Sep 2024
- Mode
- Duration
- Fees
- Full Time
- 12 months
- £17,710 in 2024/25
- Full Time
- 18 months with Professional Placement*
- £19,485 in 2024/25
Award: MSc
Starting: Jan 2025
- Mode
- Duration
- Fees
- Full Time
- 12 months
- £17,710 in 2024/25
- Full Time
- 18 months with Professional Placement*
- £19,485 in 2024/25
Professional Placement option*
The Professional Placement option will allow you to complete a credit bearing, 20 week Professional Placement as an integral part of your Master’s Degree. The purpose of the Professional Placement is to improve your employability skills which will, through the placement experience, allow you to evidence your professional skills, attitudes and behaviours at the point of entry to the postgraduate job market. Furthermore, by completing the Professional Placement, you will be able to develop and enhance your understanding of the professional work environment, relevant to your chosen field of study, and reflect critically on your own professional skills development within the workplace.
You will be responsible for finding and securing your own placement. The University, however, will draw on its extensive network of local, regional and national employers to support you in finding a suitable placement to complement your chosen area of study. You will also benefit from support sessions delivered by Careers+ as well as advice and guidance from your School.
Placements will only be confirmed following a competitive, employer-led selection process, therefore the University will not be able to guarantee placements for students who have registered for the ‘with Professional Placement’ course. All students who do not find a suitable placement or do not pass the competitive selection process will be automatically transferred back to the standard, non-placement version of the course.
Personal statement
You’ll need to submit a personal statement as part of your application for this course. This will need to highlight your passion for postgraduate study – and your chosen course – as well as your personal skills and experience, academic success, and any other factors that will support your application for further study.
Not sure what to include? We’re here to help – take a look at our top tips for writing personal statements and download our free postgraduate personal statement guide for further advice and examples from real students.
Course in Depth
Module
In order to complete this course a student must successfully complete all the following CORE modules (totalling 180 credits):
Digital forensic investigation techniques are an essential part of the body of knowledge of every cyber security specialist. They facilitate informed timely management of cyber security breaches. Their understanding is important to develop and deploy effective controls for monitoring, detecting and responding to information security incidents within the scope of criminal, civil and enterprise investigations.
The module provides you with an opportunity to learn and critically reflect on the skills of Advanced Ethical Hacking and information security within a global context. This module builds on the knowledge and underpinning theory from the networking modules and reviews the requirements for a secure network communication system.
This module prepares you for the research project that you will undertake towards the end of your master’s course. It equips you with knowledge and transferable skills that will also help you in your subsequent career, for example, when you are asked to write a report or to carry out an IT project. You will become familiar with the research literature in your discipline, research methodology and research ethics, as well as project management tools, methods and techniques.
This module aims to introduce learners to the security of Cyber-Physical Systems (CPS). Taking a holistic approach, the module will cover both operational and information technology (OT and IT) aspects of the CPS. The module will enable learners to familiarise with the state of the art with respect to CPS security through research-informed curriculum and engagement with the cutting-edge during the module. Specifically, the module will include introduction to unique security requirements for such systems, identify cyber security threat landscape for CPS, and include discussions around methods and mechanisms to protect against security threats along with codes of practice and standards used in different industries such as Manufacturing, Power, Automotive or Medical.
The module covers information security governance and its associated body of knowledge and aims to develop your technical competence in information assurance. Security measures for adequate protection of valuable information assets are essential to guard business success, reputation, and compliance with legal and regulatory requirements. This module provides students with in-depth knowledge and understanding of the concepts, methods, processes, tools and practices underlying good information security governance. Topics to be covered include security governance, risk management, security programme development and management, legislation, policies, standards, frameworks, and issuing bodies, business continuity and cybercrime.
This module covers the concepts and techniques of applied artificial intelligence (AI), focusing on the machine learning applications in practice. It provides the underpinning principles on the design and development of AI to address emerging challenges in the cyber world. A range of machine-learning schemes are examined, including identification of anomalous situations that alter data reliability and integrity. In addition, the students will develop related analytical and practical skills that can be applied in designing AI for data processing applications.
The purpose of the module is to enable you to undertake a sustained, in-depth and research-informed Level 7 project exploring an area that is of personal interest to you. In agreement with your supervisor, you will decide upon your topic which will take the form of a practical outcome (artefact) with accompanying contextual material. The main consideration when choosing your topic is that it must be aligned to the programme you are studying and informed by the research strategy of your school, and you should consider the relevance of this topic to your future academic or professional development.
Professional Placement (optional)
In order to qualify for the award of MSc Cyber Security with Professional Placement, a student must successfully complete all of the Level 7 modules listed above as well as the following Level 6 module:
This module is designed to provide you with the opportunity to undertake a credit bearing, 20-week Professional Placement as an integral part of your Master’s Degree.
The purpose of the Professional Placement is to improve your employability skills which will, through the placement experience, allow you to evidence your professional skills, attitudes and behaviours at the point of entry to the postgraduate job market. Furthermore, by completing the Professional Placement, you will be able to develop and enhance your understanding of the professional work environment, relevant to your chosen field of study, and reflect critically on your own professional skills development within the workplace.
Download course specification
Download nowThe MSc is normally studied over one year full-time or two years part-time.
The course is divided into taught modules of 20 credits and a Master’s project of 60 credits. Students complete 60 credits for Postgraduate Certificate, 120 credits for Postgraduate Diploma and 180 credits for the full MSc. Each credit represents 10 notional hours of student learning and assessment.
A range of assessment methods are employed, assessment criteria being published in each assignment brief. Knowledge and skills are assessed, formatively and summatively, by a number of methods: coursework, examinations (seen and unseen, open and closed-book), presentations, practical assignments, vivas, online forums, podcasts and project work.
This course is accredited by the following organisations:
Our accreditations from these bodies show employers that you have the level of knowledge and skills they need when you graduate.

BCS, The Chartered Institute for IT
This degree has been accredited by BCS, The Chartered Institute for IT. Accreditation is a mark of assurance that the degree meets the standards set by BCS. An accredited degree entitles you to professional membership of BCS, which is an important part of the criteria for achieving Chartered IT Professional (CITP) status through the Institute. Some employers recruit preferentially from accredited degrees, and an accredited degree is likely to be recognised by other countries that are signatories to international accords.

Engineering Council Accredited Degree
This degree has been accredited by BCS, The Chartered Institute for IT on behalf of the Engineering Council. Accreditation is a mark of assurance that the degree meets the standards set by the Engineering Council in the UK Standard for Professional Engineering Competence (UK-SPEC). An accredited degree will provide you with some or all of the underpinning knowledge, understanding and skills for eventual registration as an Incorporated (IEng) or Chartered Engineer (CEng). Some employers recruit preferentially from accredited degrees, and an accredited degree is likely to be recognised by other countries that are signatories to international accords.
Employability
Enhancing your employability skills
This course is designed to ensure that you are a very sought-after graduate with the necessary first-hand, practical expertise of cyber security issues as well as a rigorous academic understanding of the sector.
Globally there is a shortage of experts who can work in cyber security at this very high level, so you will focus on the important technical material you will need for effective decision-making in a highly demanding career.
You will be equipped for a range of careers requiring advanced skills, such as:
- security architect
- security analyst
- security administrator
- security manager
- incident response manager
- risk and compliance analyst.
You will have the opportunity to get support for obtaining industry recognised Professional Certifications.
Professional certification
There is considerable activity under way to help recognise the professional capability of both individual specialists and training, and continuing education provision on offer to such cyber security specialists.
For instance, new IT Certification and Career Paths are arising such as the Cisco Cyber Security Specialist certification called 'The Securing Cisco Networks with Threat Detection and Analysis (SCYBER)'.
International
Birmingham City University is a vibrant and multicultural university in the heart of a modern and diverse city. We welcome many international students every year – there are currently students from more than 80 countries among our student community.
The University is conveniently placed, with Birmingham International Airport nearby and first-rate transport connections to London and the rest of the UK.
Our international pages contain a wealth of information for international students who are considering applying to study here, including:
- Explore some of the good reasons why you should study here.
- Find out how to improve your language skills before starting your studies.
- Find all the information relevant to applicants from your country.
- Learn where to find financial support for your studies.
Facilities & Staff
Our Facilities
We are constantly investing in our estate and are currently in the process of spending £260 million on new learning facilities. This course will be taught at Millennium Point at the City Centre Campus.
The course is supported with a wide range of cutting-edge facilities in the City Centre Campus. We have a state-of-the-art computer games technology lab which contains high-performance PCs, Sony PlayStation development kits and a range of industry standard software including Unity, Unreal and a suite of professional Microsoft development tools.
We also have many open access areas where students can study together and even hire out laptops for use in these spaces and others within the university.
Within the University there are many internationally recognised research teams giving you the opportunity to collaborate with them on exciting interdisciplinary projects.

Computer networking
The laboratories are well-equipped for all our computer networking courses, as well as specialist areas for practical work such as voice-over internet protocol (VoIP), forensic and ethical hacking technologies, wireless and mobile technologies and radio frequency identification technologies to name but a few.

Software development and computer programming
There are a number of open access, software development and computer programming laboratories that can be used to develop systems and programmes, including database management systems such as MySQL, to name but a few.
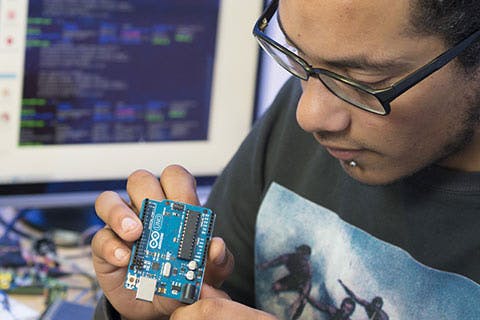
Systems laboratories
Our embedded systems laboratories are used to develop real-time systems, such as specialist hardware training and development resources, and industrial-standard software development and simulation tools. These include microcontroller software and robotics design and development, to name but a few.

Electronic systems
To underpin the basic principles of electronic systems, we have a well-equipped laboratory of general and specialist test and measurement kits, including powered prototyping development boards, dual power supplies, frequency generators and counters and digital multi-meters to name but a few.
Forensic computing
Our successful development of forensic computing has led to a specialist forensics laboratory that is fully equipped with essential hardware and software for this sensitive area of study. The laboratory includes high-spec PCs with built-in multi interface Tableau write blockers, EnCase and FTK computer forensic software and steganography detection and analysis software, to name but a few.
More on our facilities
Our staff
Professor Junaid Arshad
Deputy Head of Computing
Junaid is an alumnus of the Innovate UK & DCMS funded CyberASAP programme, commercially prototyping the CyMonD system for effective monitoring & defence of IoT-based systems against cyber-threats. Junaid has successfully achieved research funding from UK and overseas funding agencies, and has worked as a security specialist for a number of...
More about JunaidRon Austin
Associate Professor
Senior lecturer Ron Austin is the Associate Professor of the MSc Advanced Computer Networks course and teaches all network-related courses. His expertise and areas of interest include: Voice Over Internet Protocol (VoIP), security technologies, and forensic and ethical hacking.
More about RonDr Muhammad Ajmal Azad
Senior Lecturer in Cyber Security
Muhammad Ajmal Azad is a Senior Lecturer (Assistant Professor) in Cyber Security in the Department of Computer Science and Digital Technologies at Birmingham City University. His research interests broadly cover the areas of network security and privacy.
More about Muhammad Ajmal


